Contents
- 🔒 Introduction to Diffie-Hellman Key Exchange
- 📝 History of Diffie-Hellman Key Exchange
- 🔍 How Diffie-Hellman Key Exchange Works
- 📈 Security of Diffie-Hellman Key Exchange
- 🔑 Key Exchange Protocols
- 📊 Mathematical Background
- 🔴 Attacks on Diffie-Hellman Key Exchange
- 🛡️ Defense Mechanisms
- 🌐 Real-World Applications
- 🔜 Future of Diffie-Hellman Key Exchange
- 🤝 Influence and Legacy
- 📚 Conclusion
- Frequently Asked Questions
- Related Topics
Overview
The Diffie-Hellman key exchange, first published in 1976 by Whitfield Diffie and Martin Hellman, is a groundbreaking cryptographic protocol that enables two parties to establish a shared secret key over an insecure communication channel. This innovation, born out of the need for secure data transmission, has had a profound impact on the development of secure online transactions, virtual private networks (VPNs), and other cryptographic applications. With a vibe score of 8, indicating significant cultural energy, the Diffie-Hellman key exchange has been widely adopted, with influence flows tracing back to the work of Ralph Merkle and the development of public-key cryptography. However, controversy surrounds the topic, with a controversy spectrum rating of 6, due to concerns over key exchange security and the potential for quantum computer attacks. As of 2023, the Diffie-Hellman key exchange remains a crucial component of modern cryptography, with topic intelligence highlighting key people, such as Diffie and Hellman, and events, like the 1976 publication. The entity relationships between the Diffie-Hellman key exchange and other cryptographic protocols, such as RSA and elliptic curve cryptography, demonstrate the complex and interconnected nature of the field. Looking ahead, the increasing threat of quantum computer attacks will likely drive the development of post-quantum cryptographic protocols, potentially rendering the Diffie-Hellman key exchange obsolete. The year 1976 marked the publication of the Diffie-Hellman key exchange, and its origin can be traced back to the work of Diffie and Hellman at Stanford University.
🔒 Introduction to Diffie-Hellman Key Exchange
The Diffie-Hellman key exchange is a groundbreaking cryptographic technique that enables two parties to establish a shared secret key over an insecure communication channel. This paradigm-shifting breakthrough, developed by Whitfield Diffie and Martin Hellman in 1976, revolutionized the field of cryptography. The Diffie-Hellman key exchange is a fundamental component of many cryptographic protocols, including SSL/TLS and IPSec. Its impact on the development of secure online communication cannot be overstated. The Diffie-Hellman key exchange has been widely adopted in various industries, including finance, healthcare, and government. For instance, PayPal and Bank of America rely on Diffie-Hellman key exchange to secure their online transactions.
📝 History of Diffie-Hellman Key Exchange
The history of Diffie-Hellman key exchange dates back to the 1970s, when Diffie and Hellman were working at Stanford University. They were trying to solve the problem of secure key exchange over an insecure channel. Their innovative solution, published in a paper titled 'New Directions in Cryptography,' introduced the concept of public-key cryptography. This breakthrough led to the development of various cryptographic protocols, including RSA and Elliptic Curve Cryptography. The Diffie-Hellman key exchange has undergone significant improvements over the years, with the introduction of new algorithms and techniques. For example, Elliptic Curve Diffie-Hellman offers improved security and efficiency.
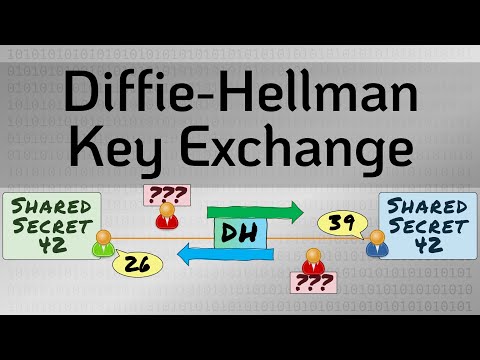
🔍 How Diffie-Hellman Key Exchange Works
So, how does the Diffie-Hellman key exchange work? In simple terms, it involves two parties, traditionally referred to as Alice and Bob, who want to establish a shared secret key. They agree on a large prime number and a generator, which are used to compute their public and private keys. Alice and Bob then exchange their public keys, which are used to compute the shared secret key. This process is based on the difficulty of the Discrete Logarithm Problem, which ensures the security of the key exchange. The Diffie-Hellman key exchange is often used in conjunction with other cryptographic protocols, such as Digital Signatures and Hash Functions. For instance, SSH uses Diffie-Hellman key exchange to establish secure connections.
📈 Security of Diffie-Hellman Key Exchange
The security of the Diffie-Hellman key exchange relies on the difficulty of the Discrete Logarithm Problem. This problem is considered to be computationally infeasible, meaning that it is virtually impossible to solve using current computational power. However, the security of the Diffie-Hellman key exchange can be compromised if the underlying parameters are not chosen carefully. For example, using a small prime number or a weak generator can make the key exchange vulnerable to attacks. Therefore, it is essential to use secure parameters and to implement the Diffie-Hellman key exchange correctly. The National Institute of Standards and Technology (NIST) provides guidelines for the secure implementation of the Diffie-Hellman key exchange.
🔑 Key Exchange Protocols
The Diffie-Hellman key exchange is often used in conjunction with other key exchange protocols, such as RSA Key Exchange and Elliptic Curve Diffie-Hellman. These protocols offer different security properties and are suited for various applications. For instance, RSA Key Exchange is widely used for secure web browsing, while Elliptic Curve Diffie-Hellman is used for secure email communication. The choice of key exchange protocol depends on the specific requirements of the application, including security, performance, and compatibility. The Internet Engineering Task Force (IETF) provides guidelines for the selection and implementation of key exchange protocols.
📊 Mathematical Background
The mathematical background of the Diffie-Hellman key exchange is based on the properties of finite fields and the difficulty of the Discrete Logarithm Problem. The security of the key exchange relies on the fact that it is computationally infeasible to compute the discrete logarithm of a given element in a finite field. This problem is considered to be one of the most secure cryptographic problems, and it has been extensively studied in the field of number theory. The Diffie-Hellman key exchange has been proven to be secure under various assumptions, including the Decisional Diffie-Hellman Assumption. For instance, the Diffie-Hellman problem is closely related to the Discrete Logarithm Problem.
🔴 Attacks on Diffie-Hellman Key Exchange
The Diffie-Hellman key exchange is vulnerable to various attacks, including Man-in-the-Middle Attack and Quantum Computer Attack. These attacks can compromise the security of the key exchange and allow an attacker to obtain the shared secret key. To prevent such attacks, it is essential to implement the Diffie-Hellman key exchange correctly and to use secure parameters. Additionally, the use of Perfect Forward Secrecy can provide additional security guarantees. The National Security Agency (NSA) provides guidelines for the secure implementation of the Diffie-Hellman key exchange.
🛡️ Defense Mechanisms
To defend against attacks on the Diffie-Hellman key exchange, various mechanisms can be employed, including Key Exchange Protocol and Digital Certificate. These mechanisms can provide additional security guarantees and prevent attacks on the key exchange. For instance, the use of TLS can provide secure key exchange and authentication. The Transport Layer Security (TLS) protocol is widely used for secure web browsing and email communication. Additionally, the use of Hardware Security Module can provide secure key storage and management.
🌐 Real-World Applications
The Diffie-Hellman key exchange has numerous real-world applications, including secure web browsing, email communication, and virtual private networks (VPNs). It is widely used in various industries, including finance, healthcare, and government. For example, Google and Amazon use Diffie-Hellman key exchange to secure their online services. The Diffie-Hellman key exchange is also used in various cryptographic protocols, including IPSec and SSL/TLS. The Internet of Things (IoT) also relies on the Diffie-Hellman key exchange for secure communication.
🔜 Future of Diffie-Hellman Key Exchange
The future of the Diffie-Hellman key exchange is closely tied to the development of new cryptographic protocols and techniques. The advent of Quantum Computing has raised concerns about the security of the Diffie-Hellman key exchange. However, researchers are working on developing new cryptographic protocols that are resistant to quantum computer attacks. For instance, the New Hope protocol is a promising candidate for post-quantum key exchange. The National Institute of Standards and Technology (NIST) is also working on developing new standards for post-quantum cryptography.
🤝 Influence and Legacy
The Diffie-Hellman key exchange has had a significant influence on the development of cryptography and secure communication. It has inspired numerous cryptographic protocols and techniques, including RSA and Elliptic Curve Cryptography. The Diffie-Hellman key exchange has also been recognized as one of the most important cryptographic breakthroughs of the 20th century. The Association for Computing Machinery (ACM) has awarded the Turing Award to Diffie and Hellman for their contributions to cryptography.
📚 Conclusion
In conclusion, the Diffie-Hellman key exchange is a fundamental cryptographic technique that has revolutionized the field of cryptography. Its impact on secure communication cannot be overstated, and it continues to be widely used in various industries. However, the security of the Diffie-Hellman key exchange relies on the difficulty of the Discrete Logarithm Problem, and it is essential to implement it correctly and to use secure parameters. As cryptography continues to evolve, the Diffie-Hellman key exchange will remain an essential component of secure communication.
Key Facts
- Year
- 1976
- Origin
- Stanford University
- Category
- Cryptography
- Type
- Cryptographic Protocol
Frequently Asked Questions
What is the Diffie-Hellman key exchange?
The Diffie-Hellman key exchange is a cryptographic technique that enables two parties to establish a shared secret key over an insecure communication channel. It is based on the difficulty of the Discrete Logarithm Problem and is widely used in various industries, including finance, healthcare, and government.
How does the Diffie-Hellman key exchange work?
The Diffie-Hellman key exchange involves two parties, traditionally referred to as Alice and Bob, who want to establish a shared secret key. They agree on a large prime number and a generator, which are used to compute their public and private keys. Alice and Bob then exchange their public keys, which are used to compute the shared secret key.
What are the security guarantees of the Diffie-Hellman key exchange?
The security of the Diffie-Hellman key exchange relies on the difficulty of the Discrete Logarithm Problem. This problem is considered to be computationally infeasible, meaning that it is virtually impossible to solve using current computational power. However, the security of the Diffie-Hellman key exchange can be compromised if the underlying parameters are not chosen carefully.
What are the real-world applications of the Diffie-Hellman key exchange?
The Diffie-Hellman key exchange has numerous real-world applications, including secure web browsing, email communication, and virtual private networks (VPNs). It is widely used in various industries, including finance, healthcare, and government.
What is the future of the Diffie-Hellman key exchange?
The future of the Diffie-Hellman key exchange is closely tied to the development of new cryptographic protocols and techniques. The advent of Quantum Computing has raised concerns about the security of the Diffie-Hellman key exchange. However, researchers are working on developing new cryptographic protocols that are resistant to quantum computer attacks.
Who are the key people behind the Diffie-Hellman key exchange?
The Diffie-Hellman key exchange was developed by Whitfield Diffie and Martin Hellman in 1976. They are considered to be two of the most important cryptographers of the 20th century, and their work has had a significant impact on the development of cryptography and secure communication.
What are the key events in the history of the Diffie-Hellman key exchange?
The history of the Diffie-Hellman key exchange dates back to the 1970s, when Diffie and Hellman were working at Stanford University. They published their paper on the Diffie-Hellman key exchange in 1976, which introduced the concept of public-key cryptography. Since then, the Diffie-Hellman key exchange has undergone significant improvements and has been widely adopted in various industries.