Contents
- 📚 Introduction to Two-Phase Commit Protocol
- 🔍 History and Development
- 📊 How Two-Phase Commit Works
- 🤝 Advantages and Benefits
- 🚫 Disadvantages and Limitations
- 📈 Real-World Applications
- 📊 Comparison with Other Protocols
- 🔒 Security Considerations
- 📚 Case Studies and Examples
- 🔍 Future Developments and Research
- 👥 Key Players and Contributors
- 📊 Conclusion and Summary
- Frequently Asked Questions
- Related Topics
Overview
The two-phase commit protocol, introduced in the 1980s by computer scientists such as Jim Gray and Andreas Reuter, is a widely used protocol for ensuring atomicity in distributed transactions. This protocol involves two phases: prepare and commit, which helps to prevent data inconsistencies in distributed systems. The protocol has been widely adopted in various fields, including database systems, financial transactions, and cloud computing. Despite its widespread use, the two-phase commit protocol has its limitations, such as increased latency and potential for deadlocks. Researchers and developers continue to explore new protocols and techniques to improve the efficiency and reliability of distributed transactions. With a vibe score of 8, the two-phase commit protocol remains a fundamental concept in computer science, with ongoing debates and innovations in the field.
📚 Introduction to Two-Phase Commit Protocol
The Two-Phase Commit Protocol is a widely used protocol in Computer Science for ensuring the consistency of transactions in Database Systems. It was first introduced in the 1970s by Jim Gray and has since become a standard in the industry. The protocol is used to ensure that multiple nodes in a Distributed System agree on the outcome of a transaction, either all committing or all rolling back. This is particularly important in Financial Transactions where data consistency is crucial. For more information on distributed systems, see Distributed Systems.
🔍 History and Development
The history of the Two-Phase Commit Protocol dates back to the 1970s when Jim Gray and his team at IBM were working on developing a reliable Transaction Processing system. They realized that a two-phase commit protocol was necessary to ensure the consistency of transactions across multiple nodes. The protocol was first described in a 1978 paper by Jim Gray and has since been widely adopted in the industry. The development of the protocol was influenced by the work of other researchers, including Edgar Codd, who developed the Relational Model for databases. For more information on the history of computer science, see History of Computer Science.
📊 How Two-Phase Commit Works
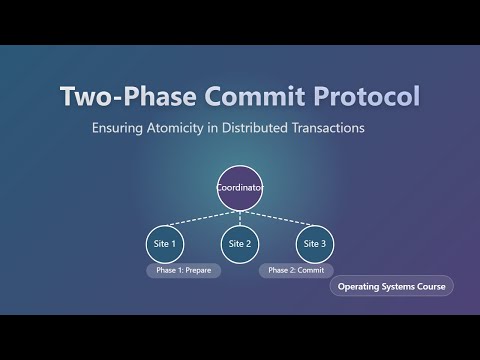
The Two-Phase Commit Protocol works by dividing a transaction into two phases: prepare and commit. In the prepare phase, each node in the system prepares to commit the transaction by locking the necessary resources and checking for any potential errors. If any node fails to prepare, the transaction is rolled back. In the commit phase, each node that successfully prepared in the first phase commits the transaction. If any node fails to commit, the transaction is rolled back. This ensures that all nodes agree on the outcome of the transaction. The protocol is often used in conjunction with Locking Mechanisms to ensure data consistency. For more information on locking mechanisms, see Locking Mechanisms.
🤝 Advantages and Benefits
The Two-Phase Commit Protocol has several advantages, including ensuring data consistency and providing a high level of reliability. It is also widely supported by most Database Management Systems. However, the protocol can be complex to implement and may require significant resources. Additionally, it can be slow due to the need for multiple nodes to agree on the outcome of a transaction. Despite these limitations, the protocol is widely used in many industries, including Finance and Healthcare. For more information on database management systems, see Database Management Systems.
🚫 Disadvantages and Limitations
One of the main disadvantages of the Two-Phase Commit Protocol is its potential for bottlenecks. If one node in the system fails to respond, the entire transaction can be delayed. This can be particularly problematic in systems where high availability is critical. Additionally, the protocol can be vulnerable to Deadlocks, where two or more nodes are blocked indefinitely, each waiting for the other to release a resource. To mitigate these risks, many systems use Timeout Mechanisms to detect and recover from failures. For more information on deadlocks, see Deadlocks.
📈 Real-World Applications
The Two-Phase Commit Protocol has many real-world applications, including Electronic Commerce and Online Banking. It is also used in Cloud Computing to ensure the consistency of data across multiple nodes. In addition, the protocol is used in Internet of Things devices to ensure the reliability of transactions. For example, in a smart home system, the protocol can be used to ensure that all devices agree on the state of the system, such as the temperature or lighting. For more information on cloud computing, see Cloud Computing.
📊 Comparison with Other Protocols
The Two-Phase Commit Protocol is often compared to other protocols, such as the Three-Phase Commit Protocol. While both protocols provide a high level of reliability, the three-phase commit protocol can be more efficient in certain situations. However, the two-phase commit protocol is more widely supported and is often easier to implement. Another protocol that is similar to the two-phase commit protocol is the Paxos Protocol, which is used in Distributed Systems to achieve consensus. For more information on the Paxos protocol, see Paxos Protocol.
🔒 Security Considerations
The Two-Phase Commit Protocol has several security considerations, including the potential for Man-in-the-Middle Attacks. To mitigate this risk, many systems use Encryption to protect data in transit. Additionally, the protocol can be vulnerable to Denial-of-Service Attacks, where an attacker attempts to overwhelm the system with requests. To prevent this, many systems use Firewalls and Intrusion Detection Systems. For more information on encryption, see Encryption.
📚 Case Studies and Examples
There are many case studies and examples of the Two-Phase Commit Protocol in use. For example, Amazon uses the protocol in its E-commerce Platform to ensure the consistency of transactions. Another example is Google, which uses the protocol in its Cloud Platform to ensure the reliability of data. For more information on e-commerce platforms, see E-commerce Platforms.
🔍 Future Developments and Research
The Two-Phase Commit Protocol is an active area of research, with many researchers exploring new ways to improve its performance and reliability. One area of research is the development of new Consensus Algorithms that can provide a higher level of reliability and efficiency. Another area of research is the use of Artificial Intelligence to optimize the protocol and improve its performance. For more information on consensus algorithms, see Consensus Algorithms.
👥 Key Players and Contributors
There are many key players and contributors to the development of the Two-Phase Commit Protocol. One of the most notable is Jim Gray, who first described the protocol in the 1970s. Another key contributor is Edgar Codd, who developed the Relational Model for databases. For more information on Jim Gray, see Jim Gray.
📊 Conclusion and Summary
In conclusion, the Two-Phase Commit Protocol is a widely used protocol in Computer Science for ensuring the consistency of transactions in Database Systems. While it has several advantages, including ensuring data consistency and providing a high level of reliability, it also has several disadvantages, including the potential for bottlenecks and vulnerability to deadlocks. Despite these limitations, the protocol is widely used in many industries and is an active area of research. For more information on database systems, see Database Systems.
Key Facts
- Year
- 1980
- Origin
- Jim Gray and Andreas Reuter's research papers
- Category
- Computer Science
- Type
- Protocol
Frequently Asked Questions
What is the Two-Phase Commit Protocol?
The Two-Phase Commit Protocol is a widely used protocol in Computer Science for ensuring the consistency of transactions in Database Systems. It works by dividing a transaction into two phases: prepare and commit. In the prepare phase, each node in the system prepares to commit the transaction by locking the necessary resources and checking for any potential errors. If any node fails to prepare, the transaction is rolled back. In the commit phase, each node that successfully prepared in the first phase commits the transaction. For more information on the protocol, see Two-Phase Commit Protocol.
What are the advantages of the Two-Phase Commit Protocol?
The Two-Phase Commit Protocol has several advantages, including ensuring data consistency and providing a high level of reliability. It is also widely supported by most Database Management Systems. However, the protocol can be complex to implement and may require significant resources. Additionally, it can be slow due to the need for multiple nodes to agree on the outcome of a transaction. For more information on the advantages and disadvantages of the protocol, see Two-Phase Commit Protocol.
What are the disadvantages of the Two-Phase Commit Protocol?
One of the main disadvantages of the Two-Phase Commit Protocol is its potential for bottlenecks. If one node in the system fails to respond, the entire transaction can be delayed. This can be particularly problematic in systems where high availability is critical. Additionally, the protocol can be vulnerable to deadlocks, where two or more nodes are blocked indefinitely, each waiting for the other to release a resource. For more information on the disadvantages of the protocol, see Two-Phase Commit Protocol.
What are some real-world applications of the Two-Phase Commit Protocol?
The Two-Phase Commit Protocol has many real-world applications, including Electronic Commerce and Online Banking. It is also used in Cloud Computing to ensure the consistency of data across multiple nodes. In addition, the protocol is used in Internet of Things devices to ensure the reliability of transactions. For example, in a smart home system, the protocol can be used to ensure that all devices agree on the state of the system, such as the temperature or lighting. For more information on real-world applications of the protocol, see Two-Phase Commit Protocol.
How does the Two-Phase Commit Protocol compare to other protocols?
The Two-Phase Commit Protocol is often compared to other protocols, such as the Three-Phase Commit Protocol. While both protocols provide a high level of reliability, the three-phase commit protocol can be more efficient in certain situations. However, the two-phase commit protocol is more widely supported and is often easier to implement. Another protocol that is similar to the two-phase commit protocol is the Paxos Protocol, which is used in Distributed Systems to achieve consensus. For more information on the comparison of protocols, see Two-Phase Commit Protocol.
What are some security considerations for the Two-Phase Commit Protocol?
The Two-Phase Commit Protocol has several security considerations, including the potential for man-in-the-middle attacks. To mitigate this risk, many systems use encryption to protect data in transit. Additionally, the protocol can be vulnerable to denial-of-service attacks, where an attacker attempts to overwhelm the system with requests. To prevent this, many systems use firewalls and intrusion detection systems. For more information on security considerations, see Two-Phase Commit Protocol.
What are some case studies and examples of the Two-Phase Commit Protocol in use?
There are many case studies and examples of the Two-Phase Commit Protocol in use. For example, Amazon uses the protocol in its e-commerce platform to ensure the consistency of transactions. Another example is Google, which uses the protocol in its cloud platform to ensure the reliability of data. For more information on case studies and examples, see Two-Phase Commit Protocol.